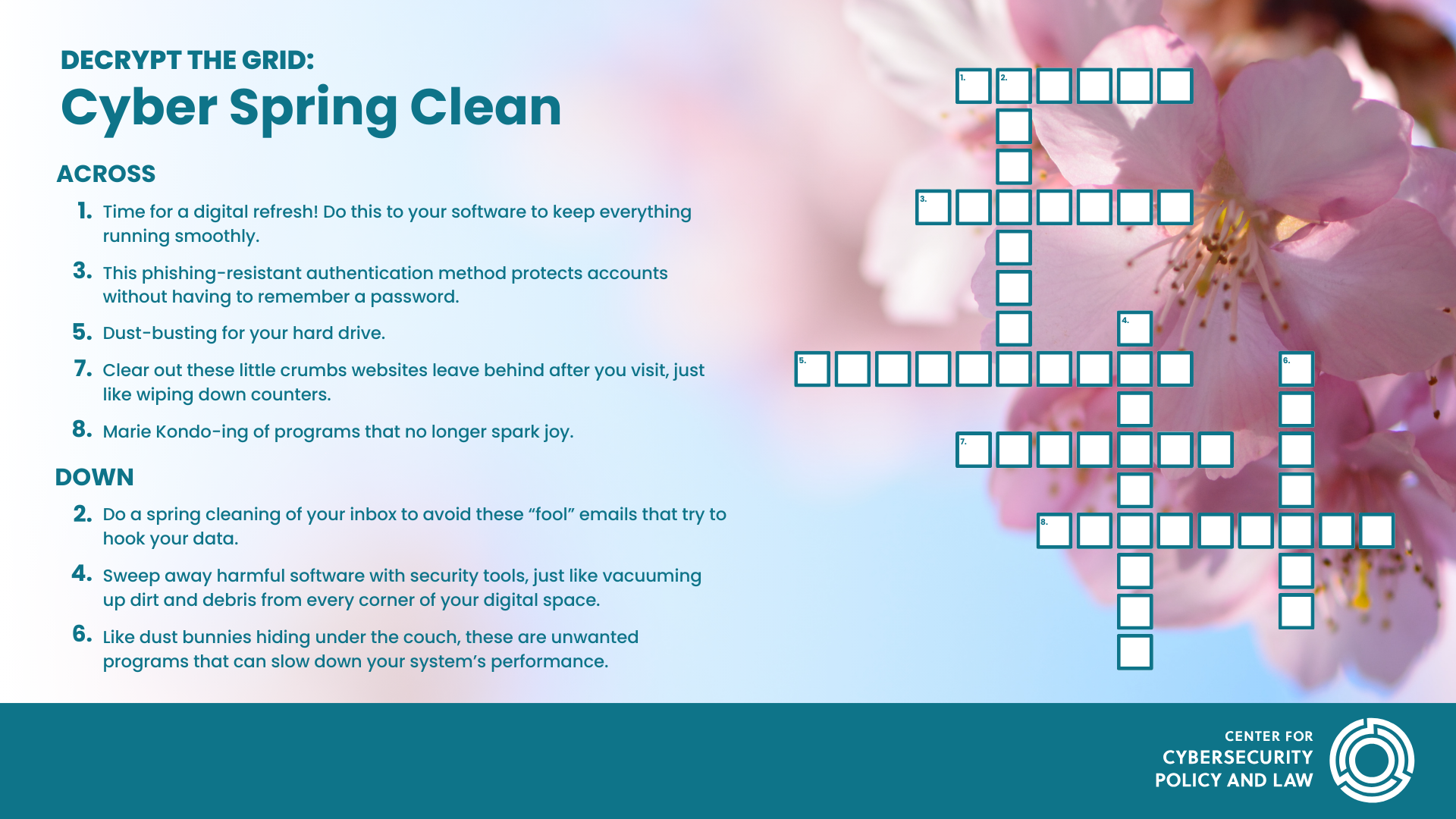
Across:
1. Time for a digital refresh! Do this to your software to keep everything running smoothly.
3. This phishing-resistant authentication method protects accounts without having to remember a password.
5. Dust-busting for your hard drive.
7. Clear out these little crumbs websites leave behind after you visit, just like wiping down counters.
8. Marie Kondo-ing of programs that no longer spark joy.
Down:
2. Do a spring cleaning of your inbox to avoid these “fool” emails that try to hook your data.
4. Sweep away harmful software with security tools, just like vacuuming up dirt and debris from every corner of your digital space.
6. Like dust bunnies hiding under the couch, these are unwanted programs that can slow down your system’s performance.
Read Next
CyberNext BRU 2026 Recap
The Cybersecurity Coalition and the Cyber Threat Alliance hosted the third annual CyberNext BRU bringing together panelists from EU institutions, industry, and academia.
Protecting Good-Faith Security Research: Building Legal Certainty Through NIS 2
Protect critical infrastructure or protect yourself. That is the untenable choice good-faith security researchers face. In much of Europe and beyond, laws still fail to clearly distinguish legitimate security research from malicious hacking.
Not All Mitigations Are Created Equal: What We are Learning from AI Vulnerability Discovery
Much has been reported on the potential looming “vulnpocolypse” but in the meantime we should be focusing on the areas where immediate resources are needed.

